SUMMARY:
Implementing robust Key Management Services (KMS) in Kubernetes establishes centralized, scalable cryptographic operations to actively secure sensitive cloud-native data and manage application secrets.
- KMS platforms use envelope encryption to strictly separate cryptographic keys from the information they protect, neutralizing threats even in the event of significant data compromises.
- Kubernetes integration natively enables etcd encryption at rest by generating data encryption keys that are subsequently secured by KMS-managed master keys.
- Successful deployments demand strategic planning for distributed architecture patterns, automated key lifecycle management, and cloud-agnostic designs to maintain comprehensive defense-in-depth.
Organizations must continuously assess and optimize their KMS architecture to maintain stringent regulatory compliance and prepare for emerging post-quantum cryptographic standards.
Table of contents
Introduction
The shift toward containerized applications and microservices architectures has fundamentally transformed how organizations handle sensitive data. Traditional security models, designed for monolithic applications and static infrastructure, are inadequate for the dynamic, distributed nature of Kubernetes environments. Key Management Services emerge as an essential component in this new paradigm, providing centralized, auditable, and scalable cryptographic operations.
Modern applications deployed in Kubernetes clusters require access to numerous secrets, including database credentials, API keys, certificates, and encryption keys. Managing these secrets securely across multiple environments, namespaces, and application lifecycles presents significant challenges. KMS addresses these challenges by providing a unified interface for cryptographic operations while maintaining separation of concerns between application logic and security infrastructure.
Understanding Key Management Services
Core Concepts
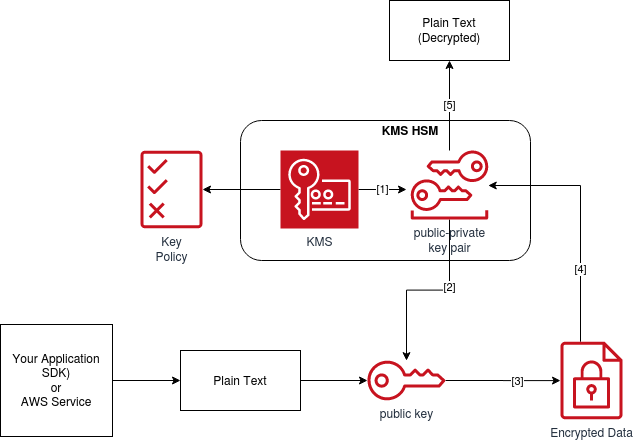
Key Management Services provide a centralized platform for creating, storing, and managing cryptographic keys used to encrypt and decrypt data. Unlike traditional secret management approaches, which store keys alongside the encrypted data they protect, KMS maintains strict separation between keys and the data they protect. This architectural principle, known as envelope encryption, ensures that even if application data is compromised, the encryption keys remain secure.
The fundamental components of a KMS include key storage, cryptographic operations, access control, and audit logging. Key storage involves securely maintaining master keys in hardware security modules (HSMs) or software-based secure enclaves. Cryptographic operations encompass key generation, encryption, decryption, and key rotation. Access control mechanisms ensure that only authorized entities can perform specific operations, while audit logging provides complete visibility into all cryptographic activities.
KMS Architecture Patterns
Enterprise KMS deployments typically follow one of several architectural patterns. The centralized model maintains a single KMS instance serving multiple Kubernetes clusters and applications. This approach simplifies key management and provides consistent security policies across the organization. However, it may introduce performance bottlenecks and single points of failure.
The distributed model deploys KMS instances closer to application workloads, reducing latency and improving availability. This pattern is particularly beneficial for geographically distributed deployments or multi-cloud environments. The hybrid approach combines centralized policy management with distributed key caching, balancing security, performance, and operational complexity.
Kubernetes Integration Architecture
etcd Encryption at Rest
Kubernetes stores all cluster data in etcd, including secrets, configuration maps, and other sensitive information. By default, this data is stored in plain text, creating significant security risks. KMS integration enables encryption at rest for etcd, ensuring that sensitive data remains protected even if storage media is compromised.
The encryption process involves generating data encryption keys (DEKs) for each secret or configuration object. These DEKs are then encrypted using key encryption keys (KEKs) managed by the KMS. The encrypted DEKs are stored alongside the encrypted data in etcd, while the KEKs remain secure within the KMS infrastructure.
KMS Provider Interface
Kubernetes implements KMS integration through a provider interface that abstracts the underlying key management system. This interface defines standard operations, including encrypt, decrypt, and status checks. The provider architecture enables organizations to integrate with various KMS solutions without modifying core Kubernetes components.
The KMS provider operates as a gRPC service, typically deployed as a DaemonSet or a static pod on control-plane nodes. This deployment model ensures high availability and minimal latency for cryptographic operations. The provider interface supports both synchronous and asynchronous operations, enabling optimized performance for specific use cases.
KMS v2 Enhancements
The latest KMS v2 specification introduces significant improvements over the original implementation. Performance enhancements include reduced API calls through improved caching mechanisms and batch operations. Security improvements encompass enhanced key derivation functions and support for additional cryptographic algorithms.
KMS v2 also introduces the concept of key hierarchies, enabling more granular control over encryption keys. This hierarchical approach supports use cases such as per-namespace encryption keys or application-specific key isolation. The specification includes provisions for key rotation without service interruption, addressing a critical operational requirement for production environments.
Implementation Strategies
Planning and Design Considerations
Successful KMS implementation begins with comprehensive planning and design. Organizations must evaluate their specific security requirements, compliance obligations, and operational constraints. Key considerations include the sensitivity of data being protected, required availability levels, performance requirements, and integration complexity.
The design phase should address key lifecycle management procedures, including generation, distribution, rotation, and destruction. Organizations must establish clear policies for key access control, defining which entities can perform specific operations on different types of keys. The design should also consider disaster recovery scenarios and business continuity requirements.
Deployment Patterns
KMS deployment in Kubernetes environments follows several common patterns. The sidecar pattern deploys KMS providers alongside application pods, providing dedicated cryptographic services with minimal latency. This approach is suitable for high-performance applications with specific security requirements.
The shared service pattern deploys KMS providers as cluster-wide services, accessible to all applications within the cluster. This model simplifies management and reduces resource overhead but may introduce performance bottlenecks for high-throughput applications. The gateway pattern implements KMS functionality through ingress controllers or service mesh components, providing additional security layers and policy enforcement.
Integration with Secrets Management
KMS integration extends beyond etcd encryption to encompass comprehensive secrets management. Modern implementations integrate with external secret management systems, providing a unified approach to handling sensitive data. This integration enables automatic secret rotation, dynamic secret generation, and centralized policy enforcement.
The integration typically involves deploying operators or controllers that interface with both KMS and external secret stores. These components continuously synchronize secrets between systems, ensuring consistency and enabling advanced features such as secret versioning and rollback.
Security Best Practices
Defense in Depth
Effective KMS security requires a layered approach that addresses multiple attack vectors. Network security controls should isolate KMS traffic through dedicated network segments or encrypted tunnels. Access controls must implement the principle of least privilege, granting only necessary permissions to specific entities.
Authentication mechanisms should leverage strong cryptographic protocols and support multi-factor authentication where appropriate. Authorization policies must be regularly reviewed and updated to reflect changing organizational requirements. Monitoring and alerting systems should detect and respond to suspicious activity in real time.
Key Lifecycle Management
Proper key lifecycle management is crucial for maintaining security over time. Key generation should use cryptographically secure random number generators and appropriate key lengths for the intended use case. Key distribution must ensure secure delivery to authorized entities without exposure to unauthorized parties.
Key rotation policies should balance security requirements with operational complexity. Automated rotation mechanisms reduce the risk of human error while ensuring consistent application of security policies. Key destruction procedures must ensure that deprecated keys are securely removed from all systems and storage media.
Compliance and Auditing
Many organizations operate under regulatory requirements that mandate specific security controls for sensitive data. KMS implementations must support compliance frameworks such as SOC 2, ISO 27001, and industry-specific regulations. Audit logging should capture all cryptographic operations with sufficient detail for compliance reporting.
Regular security assessments and penetration testing should evaluate the effectiveness of KMS controls. These assessments should include both automated vulnerability scanning and manual testing of security configurations. Documentation and training programs ensure that operational staff understand and properly implement security procedures.
Performance Optimization
Caching Strategies
KMS performance can be significantly improved through intelligent caching strategies. Local caching of frequently used keys reduces the number of remote KMS calls, improving response times and reducing network overhead. Cache invalidation policies must balance performance benefits with security requirements.
Distributed caching architectures can further improve performance in multi-node environments. Cache consistency mechanisms ensure that all nodes have access to current key material while avoiding unnecessary synchronization overhead. Cache security controls protect cached keys from unauthorized access or modification.
Scaling Considerations
KMS deployments must scale to meet the demands of growing Kubernetes environments. Horizontal scaling involves deploying multiple KMS provider instances to distribute cryptographic operations across multiple nodes. Load balancing mechanisms ensure even distribution of requests and provide fault tolerance.
Vertical scaling addresses performance bottlenecks by increasing the computational resources available to KMS providers. This approach is particularly effective for cryptographically intensive operations or high-throughput environments. Auto-scaling mechanisms can dynamically adjust KMS capacity in response to current demand.
Monitoring and Metrics
Comprehensive monitoring is essential for maintaining KMS performance and availability. Key metrics include operation latency, throughput, error rates, and resource utilization. These metrics should be collected continuously and analyzed for trends and anomalies.
Alerting systems should notify operational staff of performance degradation or security events. Alerting thresholds must be carefully tuned to avoid false positives while ensuring a timely response to genuine issues. Integration with existing monitoring infrastructure provides centralized visibility into KMS operations.
Multi-Cloud and Hybrid Strategies
Cloud-Agnostic Design
Organizations increasingly adopt multi-cloud strategies to avoid vendor lock-in and leverage best-of-breed services. KMS implementations must support cloud-agnostic designs that can operate across different cloud providers and on-premises infrastructure. This approach requires careful abstraction of provider-specific features and the creation of standardized interfaces.
Standardized APIs and protocols enable seamless integration across different environments. Organizations should prioritize solutions that support industry standards such as PKCS#11, KMIP, or vendor-neutral APIs. This approach ensures long-term flexibility and reduces migration costs.
Federation and Interoperability
Multi-cloud KMS deployments often require federation capabilities to enable secure communication between different KMS instances. Federation protocols must ensure that keys can be safely shared or synchronized across different environments while maintaining security boundaries.
Interoperability standards enable organizations to integrate KMS solutions from different vendors within a single architecture. This capability is particularly valuable for organizations with diverse technology stacks or those undergoing technology transitions. Cross-platform compatibility ensures that applications can seamlessly access cryptographic services regardless of the underlying infrastructure.
Data Sovereignty and Compliance
Multi-cloud deployments must address data sovereignty requirements that restrict where sensitive data can be stored and processed. KMS implementations should support geographic restrictions and provide clear visibility into data locations. Compliance frameworks may require specific controls for cross-border data transfers.
Regional KMS deployments can address sovereignty requirements while maintaining global operational efficiency. These deployments must balance local compliance requirements with operational simplicity and cost-effectiveness. Automated compliance monitoring ensures ongoing adherence to regulatory requirements.
Operational Excellence
Automation and Infrastructure as Code
Modern KMS deployments leverage automation and Infrastructure as Code (IaC) principles to ensure consistent, repeatable configurations. IaC templates define KMS infrastructure, policies, and configurations in version-controlled code, enabling automated deployment and change management.
Automation reduces the risk of human error and ensures consistent application of security policies. Automated testing validates KMS configurations before deployment, identifying potential issues early in the development cycle. Continuous integration and deployment pipelines enable rapid, reliable updates to KMS infrastructure.
Disaster Recovery and Business Continuity
KMS availability is critical for application operations, making disaster recovery planning essential. Recovery strategies must address both technical failures and broader disaster scenarios. Backup and recovery procedures should be regularly tested to ensure effectiveness.
Geographic redundancy protects against regional disasters and ensures service continuity. Multi-region deployments require careful consideration of data synchronization, consistency, and failover mechanisms. Recovery time objectives (RTO) and recovery point objectives (RPO) should be clearly defined and regularly validated.
Training and Organizational Change
Successful KMS implementation requires organizational change management and comprehensive training programs. Development teams must understand how to integrate KMS into their applications and workflows. Operations teams need training on KMS management, monitoring, and troubleshooting procedures.
Security teams require a deep understanding of KMS architecture, threat models, and incident response procedures. Regular training updates ensure that teams stay current with evolving technologies and threat landscapes. Documentation and knowledge-sharing practices facilitate organizational learning and capability building.
Future Considerations
Emerging Technologies
The KMS landscape continues to evolve as emerging technologies and changing security requirements emerge. Quantum computing presents both opportunities and challenges for cryptographic systems. Organizations must prepare for post-quantum cryptography transitions while maintaining current security levels.
Zero-trust architectures are driving new requirements for dynamic key management and fine-grained access controls. KMS implementations must evolve to support these architectures while maintaining performance and usability. Machine learning and artificial intelligence are being integrated into KMS solutions to improve threat detection and response capabilities.
Standardization and Industry Trends
Industry standardization efforts are driving convergence toward common KMS interfaces and protocols. Organizations should monitor these developments and align their implementations with emerging standards. Standardization reduces vendor lock-in and improves interoperability across different solutions.
Open-source KMS solutions are gaining traction, providing alternatives to proprietary systems. These solutions offer greater transparency and customization capabilities but require careful evaluation of security and support considerations. Community-driven development models can accelerate innovation but may introduce stability and compatibility challenges.
Conclusion
Key Management Services represent a critical component of modern cloud-native security architectures. Successful implementation requires careful planning, comprehensive security controls, and ongoing operational excellence. Organizations that invest in robust KMS capabilities position themselves for secure, scalable growth in increasingly complex digital environments.
The journey toward effective KMS implementation involves technical, organizational, and cultural changes. Success depends on executive sponsorship, cross-functional collaboration, and commitment to security best practices. As the threat landscape continues to evolve, KMS provides a foundation for adaptive, resilient security architectures that can meet future challenges.
Organizations embarking on KMS implementation should start with clear objectives, comprehensive planning, and phased deployment strategies. Regular assessment and continuous improvement ensure that KMS capabilities remain aligned with evolving business requirements and security threats. The investment in proper KMS implementation pays dividends through improved security posture, regulatory compliance, and operational efficiency.
Contact us for more information.

